
EC0-349 Exam Questions & Answers
Exam Code: EC0-349
Exam Name: Computer Hacking Forensic Investigator
Updated: Jul 21, 2024
Q&As: 304
At Passcerty.com, we pride ourselves on the comprehensive nature of our EC0-349 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free EC-COUNCIL EC0-349 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your EC-COUNCIL EC0-349 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free EC-COUNCIL EC0-349 Dumps
Practice These Free Questions and Answers to Pass the Certified Ethical Hacker Exam
When making the preliminary investigations in a sexual harassment case, how many investigators are you recommended having?
A. One
B. Two
C. Three
D. Four
The following is a log file screenshot from a default installation of IIS 6.0.
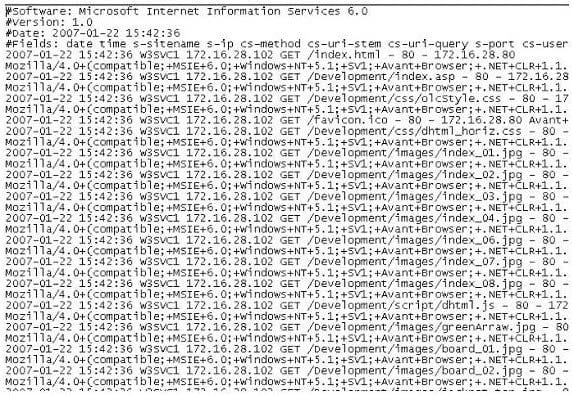
What time standard is used by IIS as seen in the screenshot?
A. UTC
B. GMT
C. TAI
D. UT
A(n) _____________________ is one that's performed by a computer program rather than the attacker manually performing the steps in the attack sequence.
A. blackout attack
B. automated attack
C. distributed attack
D. central processing attack
What does the superblock in Linux define?
A. filesynames
B. diskgeometr
C. location of the firstinode
D. available space
John and Hillary works at the same department in the company. John wants to find out Hillary's network password so he can take a look at her documents on the file server. He enables Lophtcrack program to sniffing mode. John sends Hillary an email with a link to Error! Reference source not found. What information will he be able to gather from this?
A. Hillary network username and password hash
B. The SID of Hillary network account
C. The SAM file from Hillary computer
D. The network shares that Hillary has permissions
Viewing Page 1 of 3 pages. Download PDF or Software version with 304 questions

