
312-50V7 Exam Questions & Answers
Exam Code: 312-50V7
Exam Name: Ethical Hacking and Countermeasures (CEHv7)
Updated: Jul 18, 2024
Q&As: 514
At Passcerty.com, we pride ourselves on the comprehensive nature of our 312-50V7 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free EC-COUNCIL 312-50V7 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your EC-COUNCIL 312-50V7 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free EC-COUNCIL 312-50V7 Dumps
Practice These Free Questions and Answers to Pass the Certified Ethical Hacker Exam
This tool is widely used for ARP Poisoning attack. Name the tool.
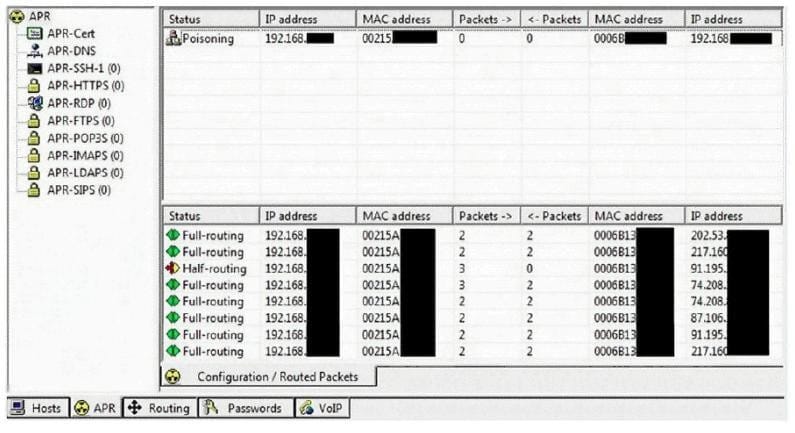
A. Cain and Able
B. Beat Infector
C. Poison Ivy
D. Webarp Infector
Choose one of the following pseudo codes to describe this statement:
"If we have written 200 characters to the buffer variable, the stack should stop because it cannot hold any more data."
A. If (I > 200) then exit (1)
B. If (I < 200) then exit (1)
C. If (I <= 200) then exit (1)
D. If (I >= 200) then exit (1)
The precaution of prohibiting employees from bringing personal computing devices into a facility is what type of security control?
A. Physical
B. Procedural
C. Technical
D. Compliance
Which security strategy requires using several, varying methods to protect IT systems against attacks?
A. Defense in depth
B. Three-way handshake
C. Covert channels
D. Exponential backoff algorithm
What is the name of the international standard that establishes a baseline level of confidence in the security functionality of IT products by providing a set of requirements for evaluation?
A. Blue Book
B. ISO 26029
C. Common Criteria
D. The Wassenaar Agreement
Viewing Page 1 of 3 pages. Download PDF or Software version with 514 questions

