
A30-327 Exam Questions & Answers
Exam Code: A30-327
Exam Name: AccessData Certified Examiner
Updated: Apr 23, 2024
Q&As: 60
At Passcerty.com, we pride ourselves on the comprehensive nature of our A30-327 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free AccessData A30-327 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your AccessData A30-327 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free AccessData A30-327 Dumps
Practice These Free Questions and Answers to Pass the ADC Exam
In FTK, which search broadening option allows you to find grammatical variations of the word "kill"such as "killer," "killed," and "killing"?
A. Phonic
B. Synonym
C. Stemming
D. Fuzzy Logic
FTK uses Data Carving to find which three file types? (Choose three.)
A. JPEG files
B. Yahoo! Chat Archives
C. WPD (Word Perfect Documents)
D. Enhanced WindowsMeta Files (EMF)
E. OLE Archive Files (Office Documents)
Using the FTK Report Wizard, which two options are available in the List by File Path window? (Choose two.)
A. List File Properties
B. Export to the Report
C. Apply a Filter to the List
D. Include Registry Viewer Reports
Click the Exhibit button.
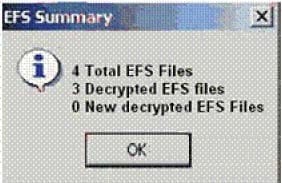
When decrypting EFS files in a case, you receive the result shown in the exhibit.
What is the most plausible explanation for this result?
A. The encrypted file was corrupt.
B. A different user encrypted the remaining encrypted file.
C. The hash value of the remaining encrypted file did not match.
D. The remaining encrypted file had previously been bookmarked.
E. An incorrect CRC value for the $EFS certificate was applied by the user.
FTK Imager can be invoked from within which program?
A. FTK
B. DNA
C. PRTK
D. Registry Viewer
Viewing Page 3 of 3 pages. Download PDF or Software version with 60 questions

