CSSLP Exam Questions & Answers
Exam Code: CSSLP
Exam Name: Certified Secure Software Lifecycle Professional Practice Test
Updated: Apr 26, 2024
Q&As: 354
At Passcerty.com, we pride ourselves on the comprehensive nature of our CSSLP exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free ISC CSSLP Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your ISC CSSLP exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free ISC CSSLP Dumps
Practice These Free Questions and Answers to Pass the ISC Certification Exam
A Web-based credit card company had collected financial and personal details of Mark before issuing him a credit card. The company has now provided Mark's financial and personal details to another company. Which of the following Internet laws has the credit card issuing company violated?
A. Trademark law
B. Security law
C. Privacy law
D. Copyright law
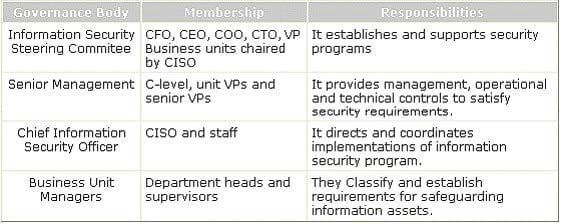
Which of the following governance bodies directs and coordinates implementations of the information security program?
A. Chief Information Security Officer
B. Information Security Steering Committee
C. Business Unit Manager
D. Senior Management
Which of the following techniques is used when a system performs the penetration testing with the objective of accessing unauthorized information residing inside a computer?
A. Biometrician
B. Van Eck Phreaking
C. Port scanning
D. Phreaking
Which of the following are the scanning methods used in penetration testing? Each correct answer represents a complete solution. Choose all that apply.
A. Vulnerability
B. Port
C. Services
D. Network
Which of the following cryptographic system services ensures that information will not be disclosed to any unauthorized person on a local network?
A. Authentication
B. Integrity
C. Non-repudiation
D. Confidentiality
Viewing Page 3 of 3 pages. Download PDF or Software version with 354 questions