
NSE7_ATP-2.5 Exam Questions & Answers
Exam Code: NSE7_ATP-2.5
Exam Name: Fortinet NSE 7 - Advanced Threat Protection 2.5
Updated: Apr 21, 2024
Q&As: 30
At Passcerty.com, we pride ourselves on the comprehensive nature of our NSE7_ATP-2.5 exam dumps, designed meticulously to encompass all key topics and nuances you might encounter during the real examination. Regular updates are a cornerstone of our service, ensuring that our dedicated users always have their hands on the most recent and relevant Q&A dumps. Behind every meticulously curated question and answer lies the hard work of our seasoned team of experts, who bring years of experience and knowledge into crafting these premium materials. And while we are invested in offering top-notch content, we also believe in empowering our community. As a token of our commitment to your success, we're delighted to offer a substantial portion of our resources for free practice. We invite you to make the most of the following content, and wish you every success in your endeavors.

Download Free Fortinet NSE7_ATP-2.5 Demo
Experience Passcerty.com exam material in PDF version.
Simply submit your e-mail address below to get started with our PDF real exam demo of your Fortinet NSE7_ATP-2.5 exam.
![]() Instant download
Instant download
![]() Latest update demo according to real exam
Latest update demo according to real exam
* Our demo shows only a few questions from your selected exam for evaluating purposes
Free Fortinet NSE7_ATP-2.5 Dumps
Practice These Free Questions and Answers to Pass the NSE 7 Network Security Architect Exam
At which stage of the kill chain will an attacker use tools, such as nmap, ARIN, and banner grabbing, on the targeted organization's network?
A. Exploitation
B. Reconnaissance
C. Lateral movement
D. Weaponization
When using FortiSandbox in sniffer-mode, you should configure FortiSandbox to inspect both inbound and outbound traffic.
What type of threats can FortiSandbox detect on inbound traffic? (Choose two.)
A. Botnet connections
B. Malware
C. Malicious URLs
D. Intrusion attempts
FortiSandbox generates structured threat information exchange (STIX) packages for which of the following threats? (Choose two.)
A. Botnet connections
B. Malware
C. Intrusion attempts
D. Malicious URLs
Which threats can FortiSandbox inspect when it is deployed in sniffer mode? (Choose three.)
A. Spam emails
B. Known malware
C. Encrypted files
D. Malicious URLs
E. Botnet connections
Examine the virtual Simulator section of the scan job report shown in the exhibit, then answer the following question:
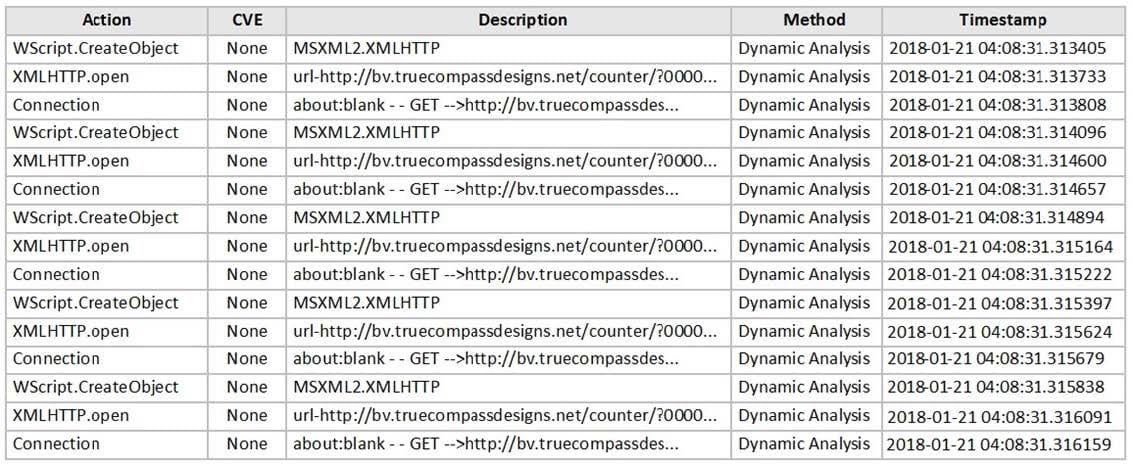
Based on the behavior observed by the virtual simulator, which of the following statements is the most likely scenario?
A. The file contained a malicious image file.
B. The file contained malicious JavaScript.
C. The file contained a malicious macro.
D. The file contained a malicious URL.
Viewing Page 1 of 3 pages. Download PDF or Software version with 30 questions

